FAQ Related Google Workspace Promo Code
Where can I find Google Workspace promo codes in 2024?
Promo codes can be found on various coupon or discussion websites like Reddit, or through Google registered affiliate partners. Mypromoinfo have a dedicated page for Google Workspace promo code where users can find ongoing promotions and discounts in 2024.
Where to enter Google Workspace promo code?
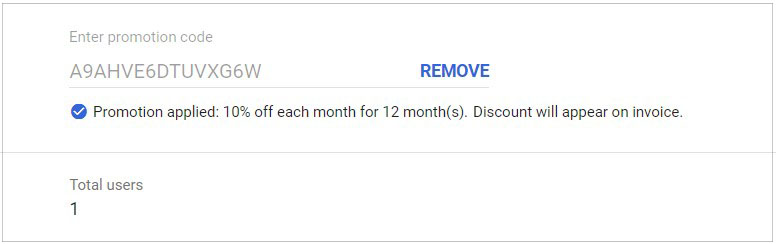
To secure a 10% discount, initially log in to your Google Workspace Admin account, then enter the promo code within the billing section of your Admin Dashboard.
Do you send legit promo code for starter and standard plans?
Yes, the promotional code we send to you is very exclusive and provided by the Google Workspace team. Each promotional code is sent out only once per customer.
Is there a guaranteed savings with a Google Workspace promo code?
Yes, the promo code we sent have guranteed savings of 10% per user per month for 12 months as of now. So go ahead and fill the form to instanly recieve Google Workspace promo code.
Can I use multiple promo codes on same Google Workspace account?
No, a promo code cannot be applied more than once if it has already been used in your account. Overall, Google Workspace Admins cannot apply a promotional discount coupon more than once.
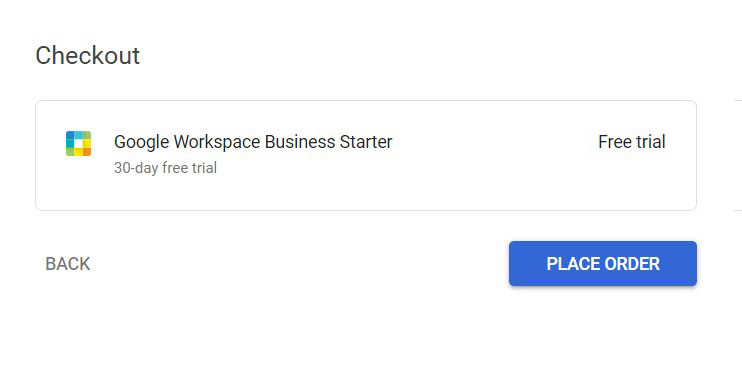
I prevailed 14 days free trial, can I still use promo code?
Yes absolutley, you can enjoy first 14 days of Google Workspace trial and after that avail additional discount to for 12 months per user.
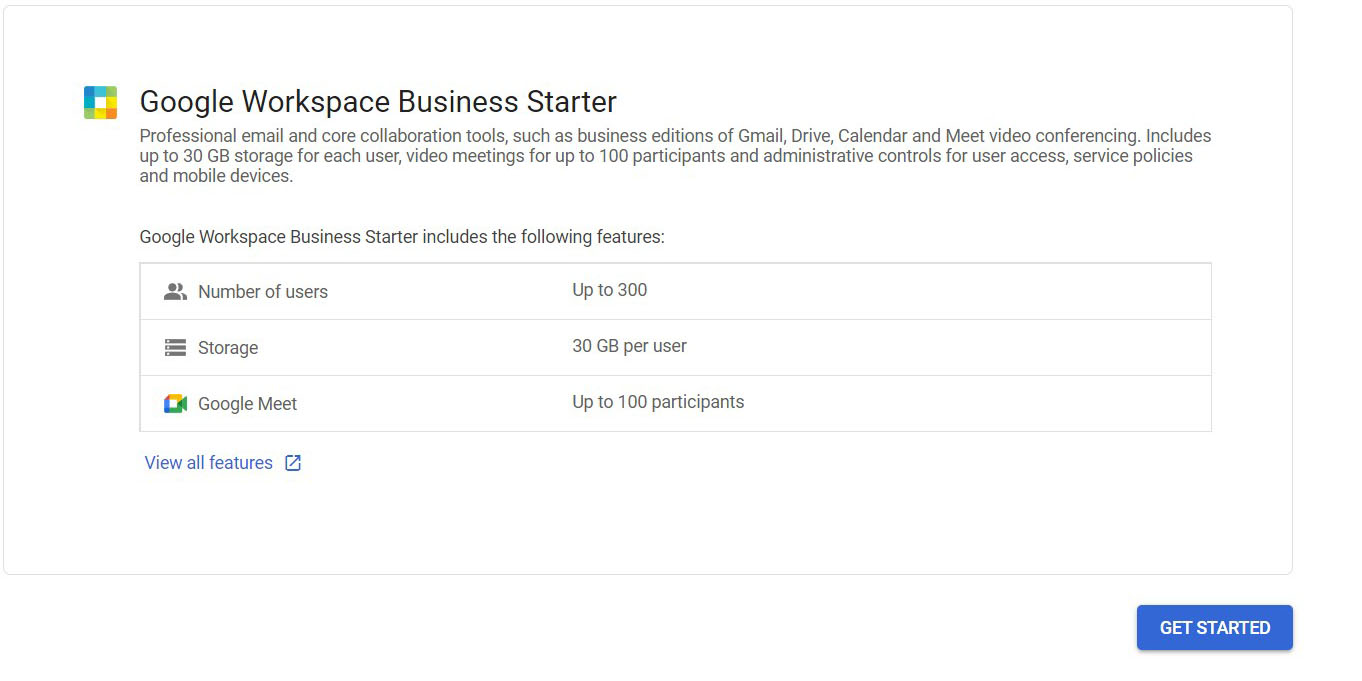
Can I use Google Workspace for free?
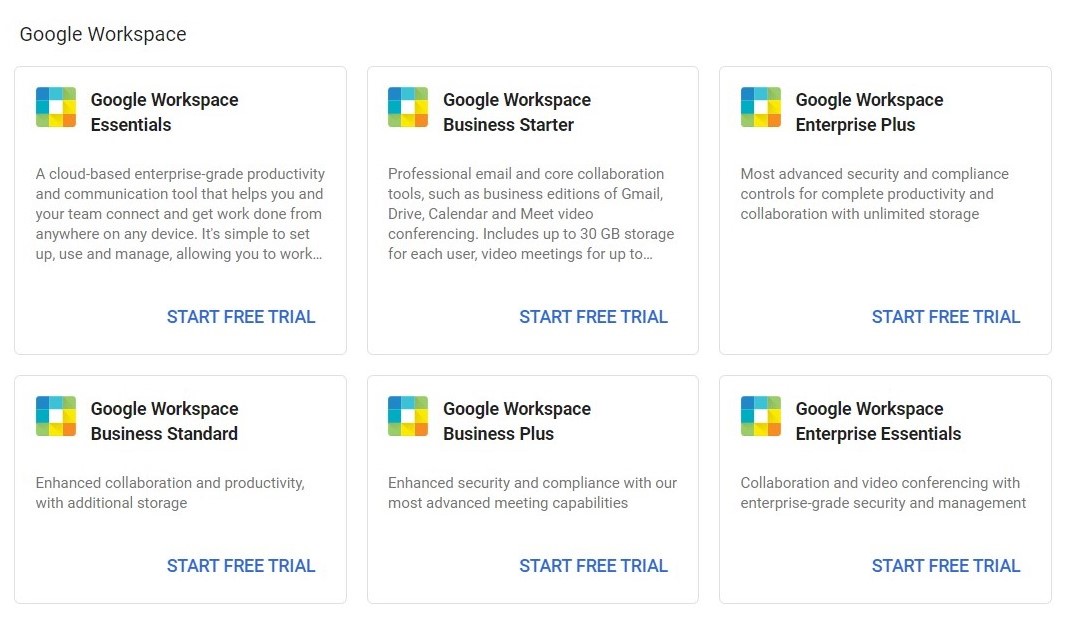
Yes, Google Workspace allows you to try their 14 days trial without any charges. You do not need to enter your credit card details to try Google Workspace. The trial does not come with any major limitations means you can try out Google Workspace services as much as you required. After 14 days trial, you may wish to continue on Google Workspace by paying monthly or annual subscription fee. In addition, there are 4 other ways to
get Google Workspace for free, check them out.
Is Google Workspace free for Students?
No, Google Workspace does not offer free access to any student. However, its offers
free access for educational institution. So signup under your school/college to check if they have Google Workspace Education access.
If I forgot to apply the promo code, will it expire?
Yes, if you recieved a promotion code from us and forget to apply it within a month or so, you cant use it anymore.
Which countries are eligible to receive discount promo code?
Currently, promo code are valid on select countries i.e, Australia, Hong Kong, New Zealand, Singapore, Indonesia, Taiwan, South Korea, Malaysia, Philippines, India, Japan, Belgium, France, Germany, Ireland, Israel, Italy, Netherlands, Portugal, Spain, United Arab Emirates, United Kingdom, Argentina, Brazil, Chile, Colombia, Mexico, Peru, Canada, United States, and Puerto Rico. If your country is listed here, you can ask us for the code.

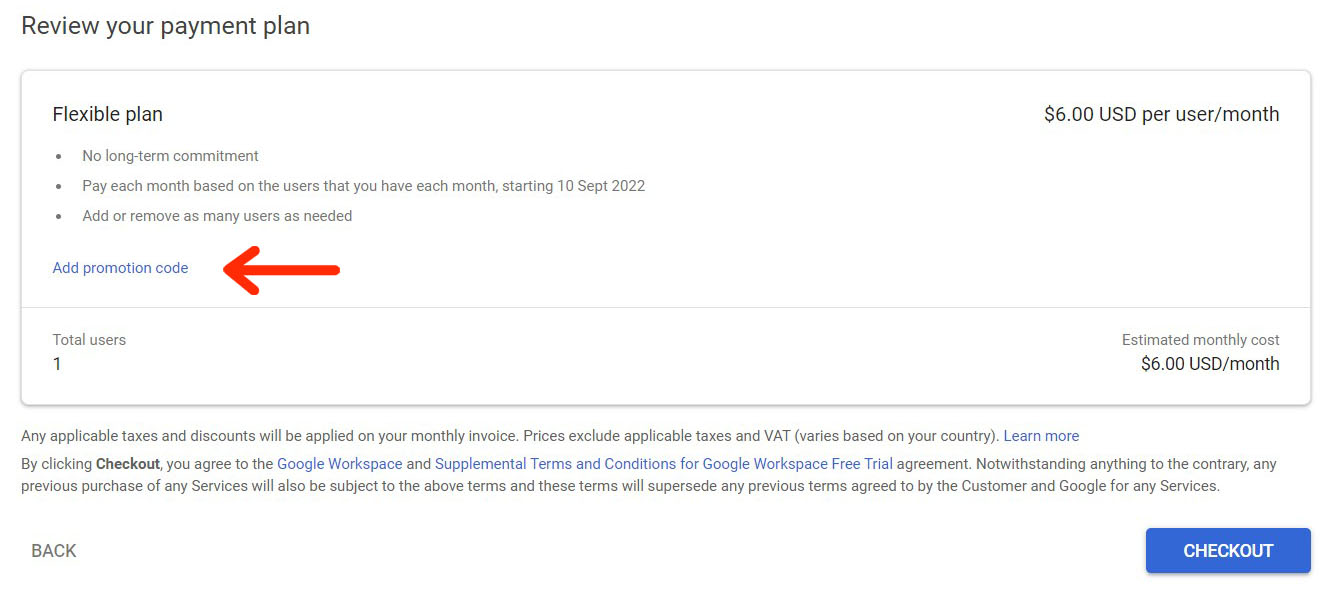
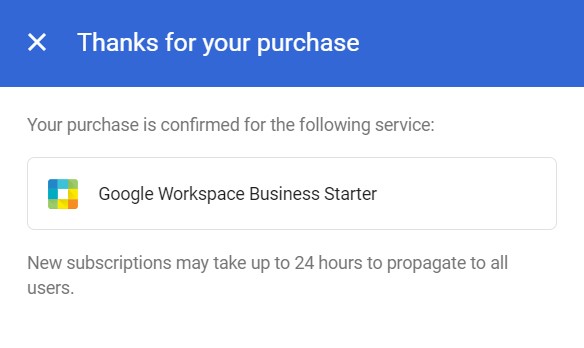 You will also get confirmation message for the same as shown above. Finally, after 14 days, use latest 2024 Google Workspace promo code to get even more discount.
You will also get confirmation message for the same as shown above. Finally, after 14 days, use latest 2024 Google Workspace promo code to get even more discount.